Welcome to the era of seamless security, where Biometric Authentication is revolutionizing the way we safeguard our digital lives. Say goodbye to the cumbersome and risky practice of juggling multiple passwords, as cutting-edge biometric technology offers a personalized key to unlock our virtual worlds—a key that’s unique to each individual: their own biological traits. From fingerprint scanning to facial recognition, this futuristic approach to security isn’t just a convenience; it’s a robust barrier against cyber threats, ensuring that your sensitive data remains under lock and key. Join us as we delve into the world of Biometric Authentication—the game-changer in password security that promises to redefine privacy and protection in our increasingly interconnected existence.
Understanding Biometric Authentication A Deep Dive Into Modern Security Measures Unpack The Basics Of Biometric Authentication And Explore How It Revolutionizes User Identification And Access Control
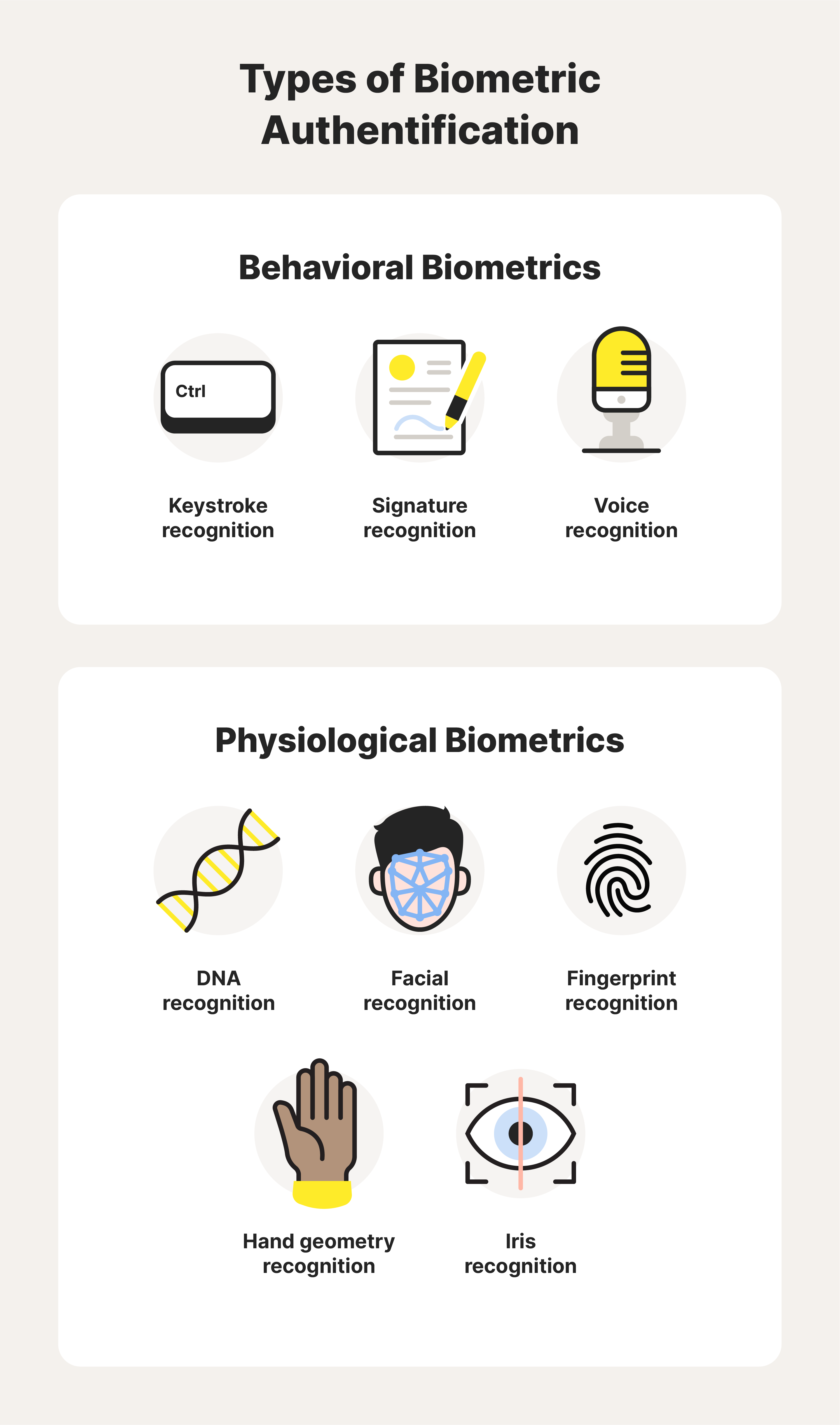
Biometric authentication is rapidly transforming the landscape of digital security, offering a personalized approach to safeguarding access. This technology leverages unique human characteristics—such as fingerprints, facial recognition, iris patterns, and voice recognition—to provide a robust layer of protection.

Unlike traditional passwords, which can be forgotten or compromised, biometric identifiers are inherently linked to an individual, making unauthorized access exponentially more challenging. By delving into the intricacies of biometric systems, we uncover a future where security measures are not only more secure but also more user-friendly, seamlessly integrating into our daily routines to create a frictionless verification process that stands at the forefront of modern security solutions..
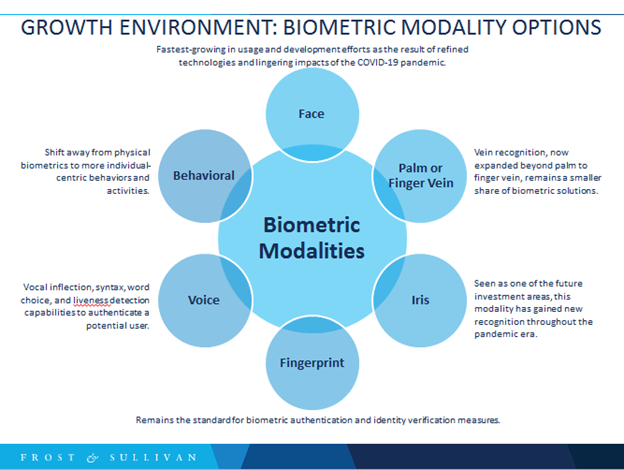
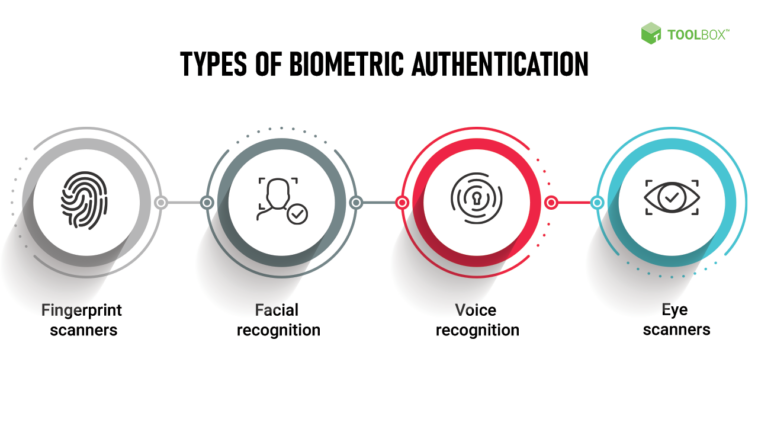
Discuss The Various Biometric Modalities Like Fingerprint Scanning Facial Recognition Iris Recognition And Voice Recognition Explaining How Each Contributes To A More Secure Future
Biometric authentication is revolutionizing password security with its advanced, user-specific modalities. Fingerprint scanning offers a unique, swift verification process, leveraging intricate patterns exclusive to each individual. Facial recognition harnesses sophisticated algorithms to analyze facial features, providing seamless access while deterring impersonation.

Iris recognition further enhances security by scanning the eye’s complex colored patterns, which are nearly impossible to replicate. Lastly, voice recognition employs distinctive vocal characteristics to ensure secure, hands-free authentication. Together, these biometric technologies embody the future of security, combining convenience with robust protection to mitigate the risks of traditional password systems..
Comparing Biometric Authentication With Traditional Password Systems Highlight The Differences Between Biometric Data And Traditional Password Systems
Biometric authentication marks a significant leap forward from traditional password systems, offering enhanced security through unique physiological characteristics. Unlike passwords that rely on recall and can be compromised or forgotten, biometric identifiers like fingerprints, facial recognition, and iris scans are inherently individualized and more difficult to replicate or steal.
This shift towards biological markers not only streamulates the login process but also reduces the risk of unauthorized access, as biometric data is intricately linked to an individual user. By integrating advanced technology that analyzes these immutable traits, biometric systems provide a robust barrier against cyber threats, placing them at the forefront of the password security evolution..
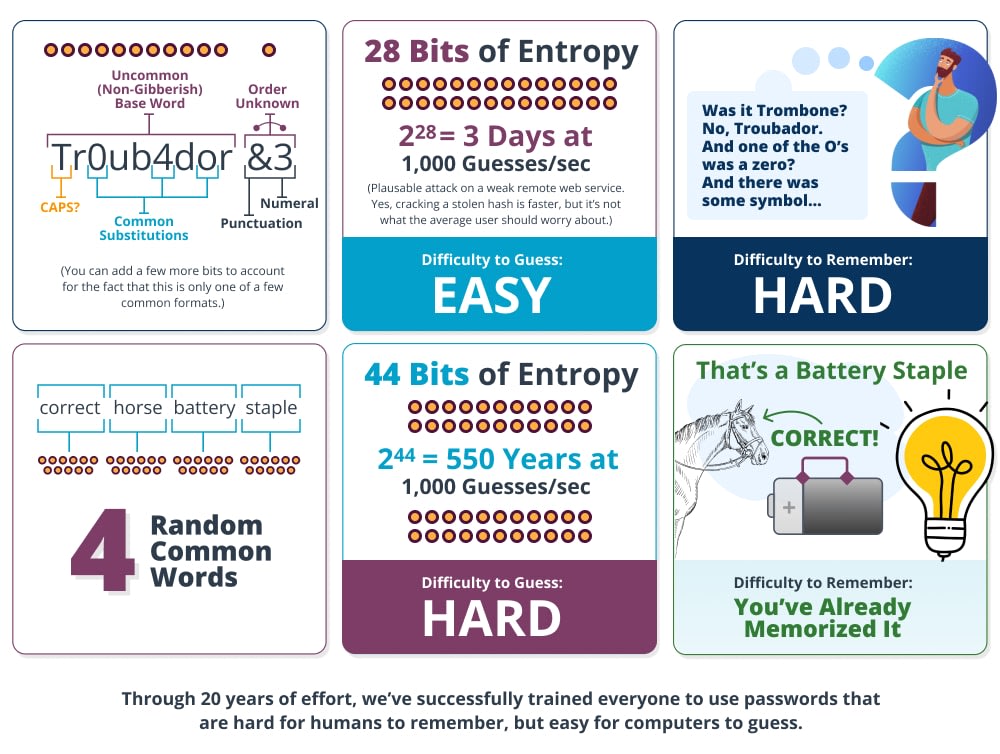
Delve Into The Limitations Of Passwords Such As Susceptibility To Theft And Forgetfulness And Explain How Biometrics Offer A More Robust And Userfriendly Alternative That Enhances Security Without Compromising Convenience
Traditional password systems are fraught with vulnerabilities, such as the risk of theft through hacking or phishing and the all-too-common issue of forgetfulness, which often leads to insecure practices like using easily guessable passwords or writing them down. Biometric authentication emerges as a formidable solution, leveraging unique physical characteristics—like fingerprints, facial recognition, or iris scans—to provide a secure and convenient access method.
This technology not only bolsters security by tying access to an individual’s immutable traits but also streamlines the user experience, eliminating the hassle of remembering complex passwords and the need for frequent resets, thus revolutionizing the way we protect our digital lives..
The Advantages Of Biometric Authentication In Everyday Life Explore Realworld Applications Of Biometric Technology From Unlocking Smartphones To Streamlining Airport Security
Biometric authentication is revolutionizing security protocols, offering robust advantages in our daily routines. The technology’s seamless integration into smartphones enables instant access with just a fingerprint or facial scan, eliminating the hassle of forgotten passwords. Moreover, at airports, biometric systems expedite check-ins, enhancing efficiency and security by swiftly verifying identities.

This cutting-edge verification method not only improves user experience by saving time but also significantly reduces the risk of identity theft, as biometric data is unique and difficult to replicate. Embracing biometric authentication is a step forward into a more secure and convenient future, where safeguarding personal information is paramount..
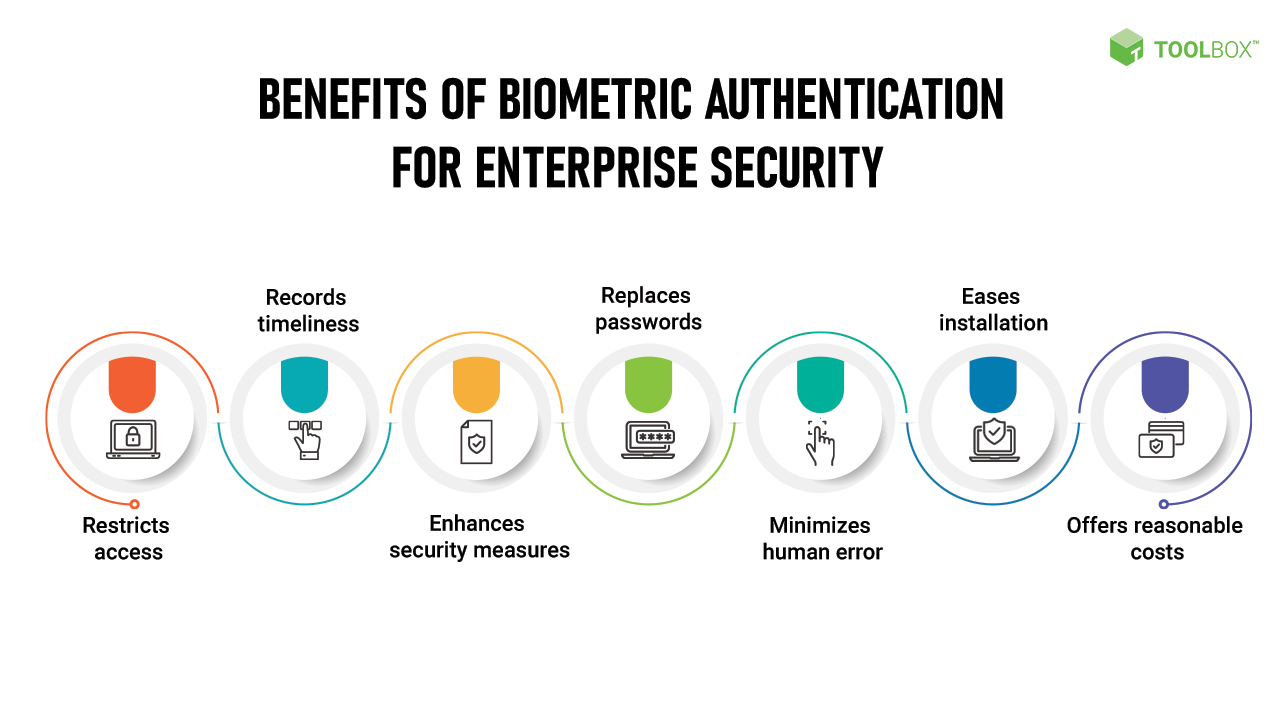
Discuss The Benefits Of Adopting Biometric Solutions Such As Improved Security Fraud Prevention And A Seamless User Experience And Provide Examples Of How This Technology Is Being Integrated Into Various Industries
Biometric authentication is revolutionizing password security by offering robust protection and a user-friendly interface. This technology leverages unique biological characteristics—like fingerprints, facial recognition, and iris patterns—to fortify defenses against fraud and hacking attempts. For instance, banking sectors have integrated biometric verification for secure transactions, while smartphones now commonly feature fingerprint or facial ID for device access.

Additionally, healthcare providers employ biometrics to safeguard patient data, ensuring compliance with privacy regulations. By adopting biometric solutions, industries are not only enhancing their security posture but also streamlining the authentication process, thereby elevating the overall user experience..
Addressing Privacy Concerns Safeguarding Biometric Data Tackle One Of The Most Critical Issues Surrounding Biometric Authenticationprivacy And Data Protection
In the realm of biometric authentication, ensuring the privacy and security of sensitive data is paramount. As we embrace this advanced password security solution, we must vigilantly protect against unauthorized access and potential breaches. Implementing robust encryption standards and strict access controls is essential for safeguarding biometric data.
Companies and institutions need to adopt transparent data policies and regularly update security protocols to maintain trust and compliance. By addressing these privacy concerns head-on, we can foster a secure environment where biometric authentication not only enhances user convenience but also fortifies the protection of personal information in the digital age..
Outline The Strategies And Technologies Used To Secure Biometric Data Such As Encryption And Secure Databases
In the vanguard of cybersecurity, safeguarding biometric identifiers demands robust strategies, leveraging advanced encryption and fortified databases. To ensure impenetrable protection, biometric data is encrypted using sophisticated algorithms, transforming sensitive information into unreadable code that only authorized systems can decipher.
Secure databases, with multi-layered access controls, act as vaults, allowing only authenticated users to retrieve or modify the fingerprint, facial recognition, or iris scan data they contain. Moreover, these databases employ real-time monitoring to detect and thwart unauthorized access attempts, ensuring that the unique physical and behavioral traits used for authentication remain solely in the hands of their rightful owners..
Explain The Importance Of Transparency And Regulations In Maintaining User Trust And Protecting Personal Information
In the evolving realm of biometric authentication, the significance of transparency and regulations cannot be overstated. As biometric data becomes integral to password security, it’s imperative that users trust the systems safeguarding their most personal information. Clear regulations and transparent practices are the bedrock of this trust, ensuring that data is not only secure but also handled ethically.
Adherence to stringent data protection laws and open communication about data usage policies help maintain user confidence. By fostering a secure environment that prioritizes privacy, technology providers can guarantee that biometric authentication is not only convenient but also a bastion of user privacy in the digital age..
The Evolution Of Password Security Whats Next For Biometrics Speculate On The Future Advancements In Biometric Technology And Its Potential To Replace Passwords Entirely
As biometric authentication technology rapidly evolves, it stands poised to redefine password security, signaling a future where digital access is seamless yet more secure than ever. Advancements in biometric identifiers, such as retina scans, heart rate patterns, and even behavioral biometrics, are on the horizon, potentially offering a unique security solution that is intrinsically tied to the user and nearly impossible to replicate.
With continuous improvements in accuracy and user-friendliness, biometrics are expected to transcend traditional passwords, providing a frictionless authentication process that could ultimately render passwords obsolete. Embracing these innovations, the security landscape is set to shift towards a more personalized and impenetrable system, ensuring data protection in an increasingly digital world..




GIPHY App Key not set. Please check settings